Introduction
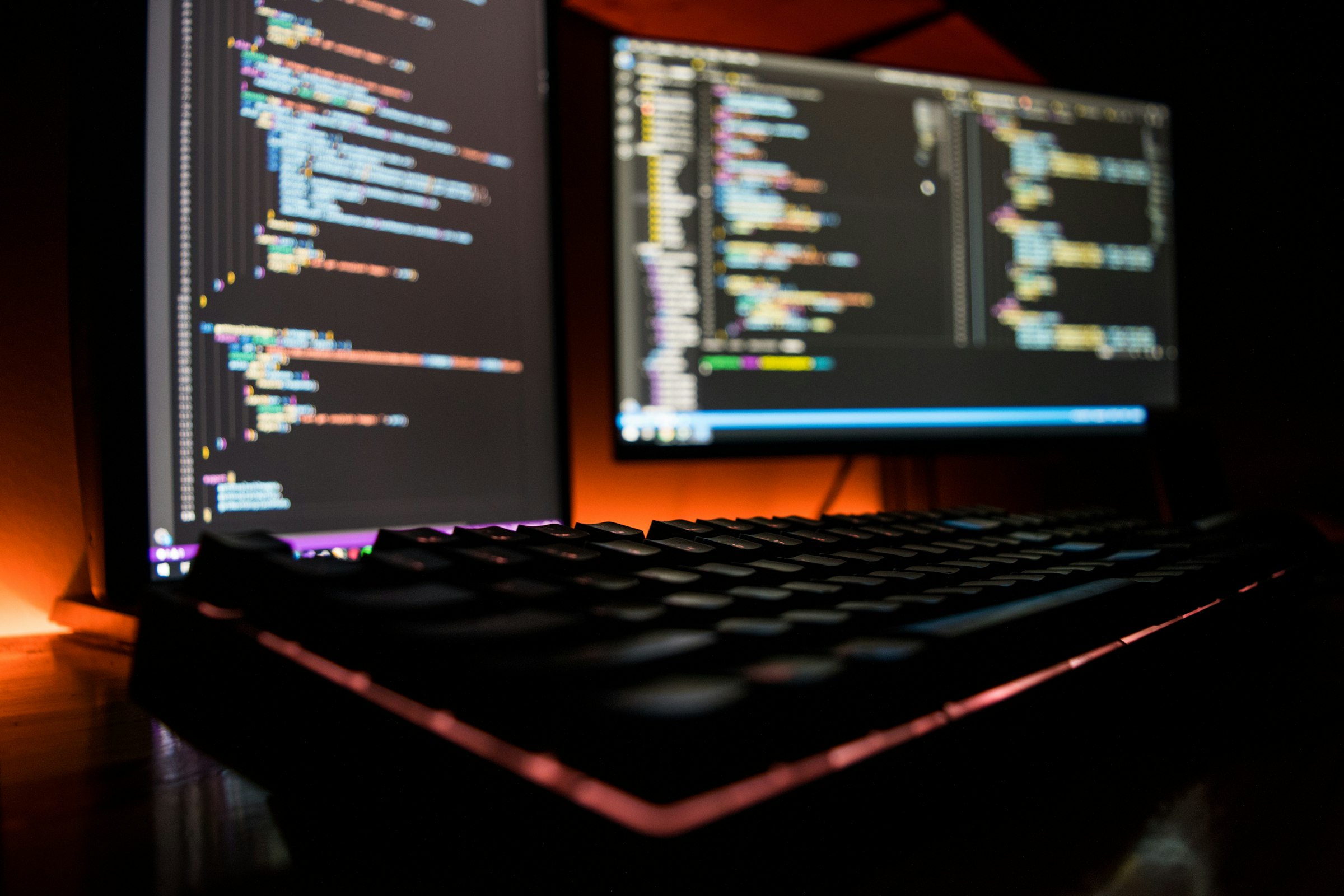
A zero-day exploit for iOS full-chain remote code execution with persistence is worth between $1 million and $2.5 million on the private market. An Android equivalent fetches $2 to $2.5 million. A Chrome RCE with sandbox escape goes for $500,000 to $1 million. These are not theoretical numbers — they are published prices from commercial exploit brokers like Zerodium and Crowdfense. Understanding this market is essential for understanding the threat landscape.
The Three Markets
The white market is bug bounty programs. Apple pays up to $2 million for zero-click kernel code execution. Google pays up to $250,000 for Chrome exploits. These programs incentivize disclosure to the vendor, and they work — Google's Vulnerability Reward Program has paid out over $50 million since inception. But bug bounty payouts are a fraction of what the gray and black markets pay.
The gray market consists of exploit brokers who purchase vulnerabilities and sell them to government agencies and law enforcement. Companies like Zerodium, Crowdfense, and (historically) Hacking Team and NSO Group operate in this space. The buyers are typically intelligence agencies and law enforcement organizations that use the exploits for surveillance and national security operations. This market is legal in most jurisdictions but ethically controversial.
The black market is criminal. Exploit developers sell to ransomware groups, cybercrime syndicates, and anyone willing to pay. Prices are lower than the gray market (a ransomware group cannot pay $2 million for an exploit), but the volume is higher and the exploitation is indiscriminate.
What This Means for Defenders
The existence of a multi-billion-dollar vulnerability market means that zero-day exploits are being used against organizations right now by actors who can afford them. You cannot patch a zero-day (by definition), so your defense must be layered: assume that any single security control can be bypassed and invest in detection and response capabilities that work even when the initial compromise succeeds.
Reduce your attack surface. Every application, every service, every protocol you expose is a potential zero-day target. Disable unnecessary services. Remove unused applications. Minimize your internet-facing footprint. The fewer targets you present, the fewer zero-days are relevant to your environment.
Vulnerability Disclosure Ethics
The security community has debated responsible disclosure for decades. Coordinated disclosure — reporting to the vendor first and allowing time to patch before public disclosure — remains the gold standard. But when vendors are slow to patch, or when exploitation is detected in the wild, the calculus changes. The goal should always be to minimize harm to end users, even when that means uncomfortable conversations with vendors about their patching timelines.