Introduction
I spent the first half of my career in IT security and the last decade increasingly focused on operational technology. The cultural divide between IT and OT is wider than the technical one, and until organizations bridge that gap, their critical infrastructure will remain vulnerable.
Why OT Security Is Different
In IT, the security priority is confidentiality, then integrity, then availability (CIA). In OT, it is reversed: availability first, then integrity, then confidentiality (AIC). A water treatment plant does not care if someone reads the sensor data — they care if someone changes the chlorine dosage or shuts down the pumps. This fundamental difference in priorities shapes every security decision.
OT systems have decades-long lifecycles. The PLC controlling a manufacturing line might run Windows XP Embedded and have been installed in 2008 with no patches since 2012. It cannot be patched because the vendor no longer supports it, and it cannot be replaced because the cost of retooling the production line is $10 million. You have to secure it as it is, not as you wish it were.
The Convergence Problem
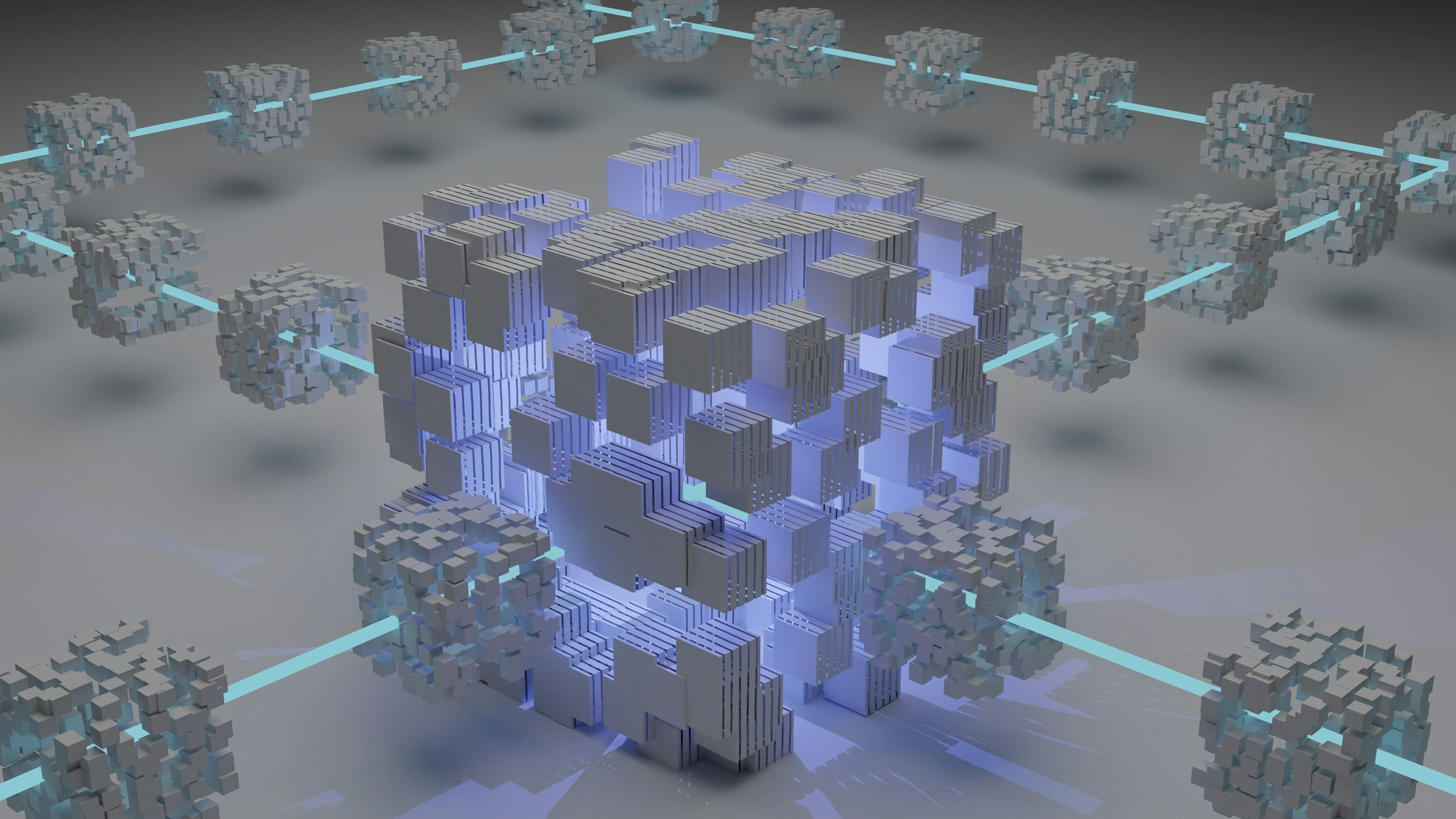
IT and OT networks used to be air-gapped — physically separated with no data flow between them. That era is over. Modern OT environments require connectivity for remote monitoring, predictive maintenance, supply chain integration, and data analytics. Every connection is a potential attack path from the IT network (which faces the internet) into the OT network (which controls physical processes).
The Purdue model provides a reference architecture for segmenting IT and OT: Level 0-1 is the physical process and controllers, Level 2 is supervisory control, Level 3 is manufacturing operations, Level 3.5 is the demilitarized zone between IT and OT, and Levels 4-5 are enterprise IT. The DMZ between Level 3 and Level 4 is the critical security boundary — all traffic between IT and OT should pass through it, and nothing should traverse it without inspection.
Practical Security Steps
Network visibility is the foundation. You cannot secure what you cannot see. Deploy passive network monitoring (Claroty, Nozomi Networks, Dragos) that can identify OT assets, map communication flows, and detect anomalies without interfering with sensitive industrial protocols. Active scanning is risky in OT — a malformed packet can crash a PLC that has been running for years.
Implement strong authentication at the IT-OT boundary. Multifactor authentication for all remote access into OT networks. Separate credentials for OT access — do not use the same Active Directory accounts for IT and OT access, because an IT-side compromise immediately extends into OT.
Build relationships between IT security and OT engineering teams. They speak different languages, have different priorities, and work under different constraints. Joint tabletop exercises, cross-training programs, and shared incident response plans are investments that pay dividends when an incident occurs.